I hope you’ve got your popcorn ready, this week was a doozy. I spent most of my week doing company events in San Francisco, but that didn’t stop me from keeping up with some absolutely ridiculous events around the internet, including the xz backdoor, another sleazy data broker, an update to the AT&T breach, and some unsubstantiated noise clouding Signal.
I even managed to find time to work on my site some more, addressing a couple points of feedback, and adding a completely overkill feature that is just cool.
XZ Backdoor
I feel like we just have to start with the xz backdoor – even though it only came to light on Friday, it immediately captured my whole attention and I hardly remember anything that happened before Friday.
For those who haven’t been following the saga, the gist of it is that a maintainer of the popular xz package, which is used for compression/decompression by a variety of upstream programs, attempted to ship an update to the package that would inject a NOBUS backdoor authorization mechanism when used in the context of sshd.
To catch up on what is going on, I highly recommend Evan Boehs’ “Everything I Know About the Xz Backdoor.” In it, he covers the timeline of the user, Jia Tan, including some other suspicious behavior going back to 2021.
We know that Kali and Homebrew were both impacted, as well as have ideas of other impacted distros. Some other interesting theories that I’ve seen involve very abnormal commit times and potential co-conspirators. I think it remains to be seen if the developer was complicit, compelled, or compromised, though many minds smarter than I are definitely leaning towards “complicit.” I suppose only time will tell.
Technical analysis is still ongoing, but what we’ve seen so far is quite interesting. One of the findings that especially surprised me is this stray dot that somehow led to a sandbox not being used. I don’t pretend to understand enough about it, but that’s such a simple diff that I would have never thought to attempt.
People Data Labs
I saw an interesting twitter thread while I was totally absolutely paying complete attention in a work session about a sophisticated phishing attack that relied on a lot of existing information and Caller ID spoofing. What stood out to me about this thread wasn’t the phishing attack details, but rather the reference to People Data Labs.
I’ve spent a pretty good amount of time trying to hunt my personal information off the internet from various data brokers. I remember using an old version of Delete Me’s Opt Out Guides probably close to 10 years ago now. But I had never heard of this People Data Labs, so I was curious.
They purport to be a business to business “people enrichment” service, providing additional context about people. From what I can tell, “business to business” in this sense means due diligence going so far as “Owns a domain name,” and no farther. Within a few minutes I had my free account and was able to look up myself and some friends who gave me consent to look them up.
While pulling the data, I noticed this remarkable API design, where they just have you run a sql query against a data set and then return the results to you. The /v5/ in the URL is what makes it super funny to me, though. Five iterations of the API to land on “Just send us SQL, we’ll figure it out.”
As far as the data this broker has, it seems like it may have been primarily scraped or collected from other data brokers as a sort of aggregation. They had very little information on me – one old email address, a phone number that belonged to my dead grandparents, and an address that belonged to my other grandparents a little over a decade ago. That’s about all they had on me. But they had much more on my friend, which appeared to heavily rely on Facebook and Linkedin scraping, combined with company enrichment data from a site like ZoomInfo.
Overall, these companies are parasites and deserve to have their business destroyed. But short of being able to single handedly destroy their business, I’d recommend requesting them to delete your data. I’ve also gone ahead and submitted them to Yael Grauer’s BADBOOL list.
If manually submitting opt out requests sounds exhausting, there are multiple services that will do it for you on an ongoing basis for an annual fee. I don’t personally use them, since I’m the type of nerd that enjoys opting out myself. But I have made many recommendations for Delete Me and it has worked well for the folks who use it and don’t want to think about it.
AT&T Admits It’s Their Data
Following up on the data breach I touched on in last week’s retro, AT&T has admitted that their data was leaked, though they still can’t say if they were breached or if it originated from a partner.
TechCrunch also reported that bulk account passcode resets were sent out, since the passcodes were also included in the leaked data. I can’t say I’m surprised to see Chick3nman quoted as the researcher, and it’s pretty funny that they normalized the encryption of all passcodes, such that there were only 10,000 unique encrypted values. It makes sense if you want to save database size by normalizing the encrypted passcodes into their own table. But if they were stored inline on the table, then there was no reason to not uniquely encrypt each passcode such that there were never duplicates.
As always, Have I Been Pwned can let you know if your data was breached, but only if you know which email address you used for AT&T or AT&T affiliated services.
Signal 0-Click? Not Likely
I was really on the fence about even including this, but I think it deserves addressing, not because there is any merit to it, but rather because of the way people responded to it.
A user, Adam Donenfeld, tweeted about a strange experiencethey had with Signal. In their thread, they suggest that it’s likely a 0-click exploit attempt (fully acknowledging it’s a conspiracy theory). They then go on to recommend people uninstall Signal.
I think we should always be wary of people who are advocating for uninstalling software that has a proven track record. I’m not suggesting there are no bugs in Signal. Hell there could even be a 0-click exploit for it. But Signal has a track record of taking the security and privacy of it’s users far more serious than any alternative. This can be seen in their response to a subpoena in 2021, the only data they could produce for a phone number was last connection date and account created date.
If this wasn’t bad enough, then others piled on, amplifying the noise (read: FUD) around Signal. They observed some mildly strange behavior and leaned into the “It must be a 0day against little old me” mentality.
Signal president Meredith Whittaker came out and says it corresponds to a bug in their phone number privacy/username implementation and that a fix will be out soon. Naturally, the FUD spreaders move the goal posts and put it on Signal to prove with certainty that it’s not a 0-click exploit. Meanwhile Adam never sent the logs / crash dumps to Signal, so Signal is doing the best with what they’ve got. Adam’s subsequent resistance to sending logs to Signal further raises my suspicions.
I think it is not only suspicious to engage in this bad faith FUD spreading, but borderline insane. If I assumed that every time one of my computing devices did something weird, I was getting 0-click exploited, I’d personally have had hundreds of millions of dollars worth of bugs burned against me. And that’s the type of grandiose delusions that I just can’t subscribe to.
Site Updates
Feeds
A few people last week asked about RSS feeds for my weekly retro. My site actually supports automatically generated RSS feeds for all of my tags, in addition to the main blog RSS feed. But this fact wasn’t particularly well known since nowhere on the site linked to it. So I’ve updated the “term” pages, that Hugo uses to list all pages that match a particular term, to include RSS and JSON Feed links in the header. This should hopefully make it easier to subscribe to only the things you’re interested in, rather than subscribing to whatever whims I decide to act on throughout the week. Here’s where you can subscribe to only the weekly retros .
Site Search
I also worked on a search feature for my site, which you can currently access with ctrl/cmd + k. I have had a bit of an obsession with command bars for quite some time now, and decided I wanted to add one to my site.
It uses elasticlunr to power in-browser search across my whole site, using a custom “search index” output that I built for Hugo. There are definitely some areas for improvement that are still to come, but I’m happy with how far I made it based entirely on “I think this would be cool” and then working on it in the evenings after my extra-long work days throughout the week.
Book Shortcodes
As you’ll see below in my “What I’m Reading” section, I started working on a book shortcode that lets me highlight what I’m reading, along with some comments about the book. I think this adds a nice way to break up the current format of “wall of text”. I’d like to further improve this shortcode by loading from a json data file and adding a progress bar so you can see how far into the book I am.
What I’m Reading
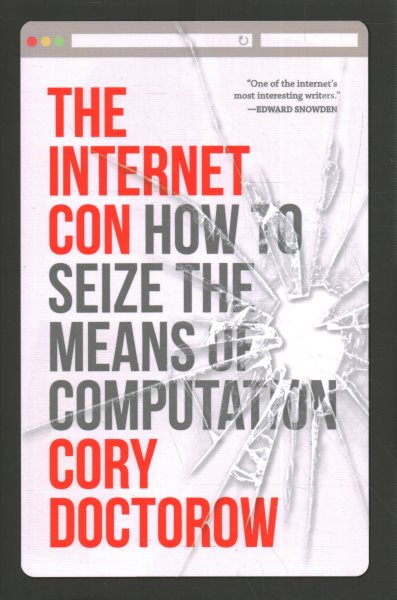
The Internet Con
By Cory Doctorow
ISBN: 978-1-80429-124-5Learn More
After finishing Red Team Blues, I switched gears to The Internet Con, which is a non-fiction book tackling Big Tech and interoperability. I’m only a few chapters in so far, but I am not surprised that it is resonating with me and my desire to own my own internet presence.
Interesting Links
- ostree - I was reminded this week of the ostree project, which seeks to make deploying bootable filesystem trees a git-like experience. This allows for some incredibly powerful features, such as transactional upgrades and rollbacks for the entire system. This project is quite old, with the oldest commit on Github going back to Jun 12, 2012. But the idea is fascinating and I think it is similar in nature to NixOS and Home Manager.
- Timewall - A “rewrite it in rust” implementation of MacOS style dynamic wallpapers, for GNU/Linux. I’m a big fan of these dynamic wallpapers and their follow-the-sun model on my Mac, so I’m excited to be able to have them elsewhere as well.
- Customized Aerial Screensaver - Similar to how I like the dynamic wallpapers on MacOS, I also like the aerial screensavers (mine flies over the Bay Bridge and into San Francisco). But I would love to be able to customize it, maybe with the custom da vinci virus render I commissioned from years ago.
- Local-first Software - This is a philosophy about how you should own your data, not the cloud, and an advocacy for developing apps that use Conflict-free Replicated Data Types (CRDTs) to enable local-first software with first-class collaboration features.
- File over app - This is similar to the previous link, but the philosophy that digital artifacts should be files you can control, in formats that are easy to retrieve and read.
Upcoming Projects
- I am working on a talk idea that I’d like to submit to BSides Las Vegas. (Due: 2024-04-21)
- I am toying with the idea of submitting a training around docker and dependency management to OWASP Global AppSec. (Due: 2024-05-06)
- I am interested in applying for the Defcon 32 Call for DJs to do a nerdcore show at Defcon this year. (Due: 2024-06-01)
- I am working on a new song, produced by Mikal kHill. (Due: N/A)
